Malware analysis Suspicious activity
4.6
$ 34.99
In stock
(742)
Product Description

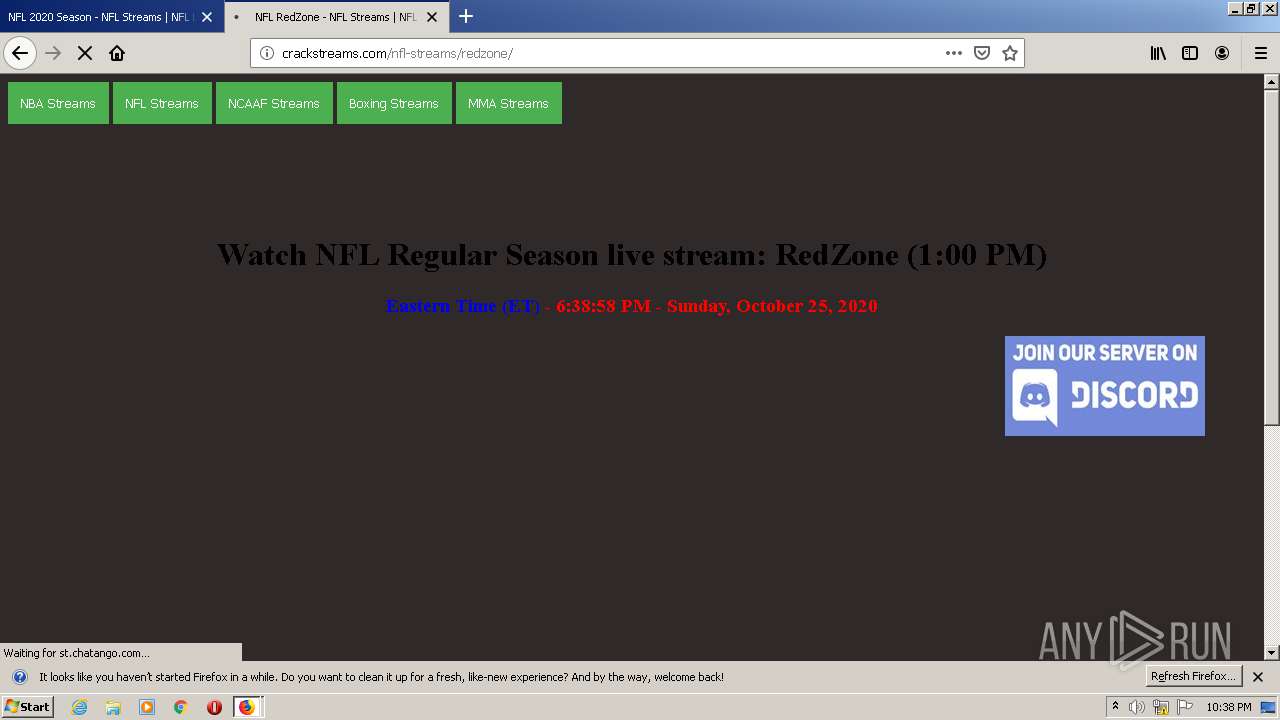
Malware Analysis: Steps & Examples - CrowdStrike
Highlight, take notes, and search in the book

Mastering Malware Analysis: A malware analyst's practical guide to combating malicious software, APT, cybercrime, and IoT attacks, 2nd Edition
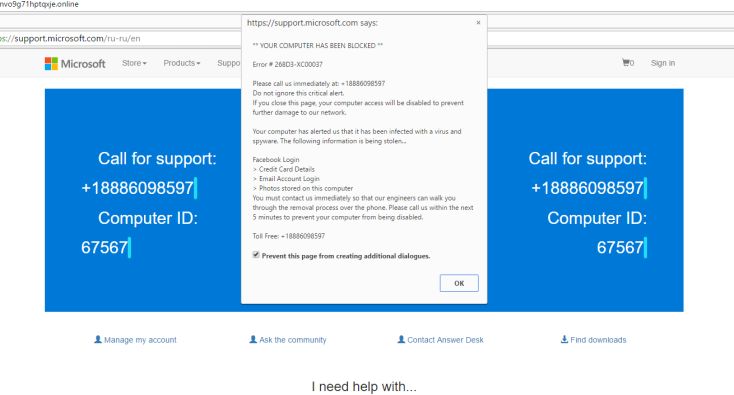
Remove You May Have Suspicious Activity On Your PC Fake Alert

Malware Analysis: Tips & Tricks Poster

Operation Triangulation: iOS devices targeted with previously

Intro to Malware Analysis: What It Is & How It Works - InfoSec

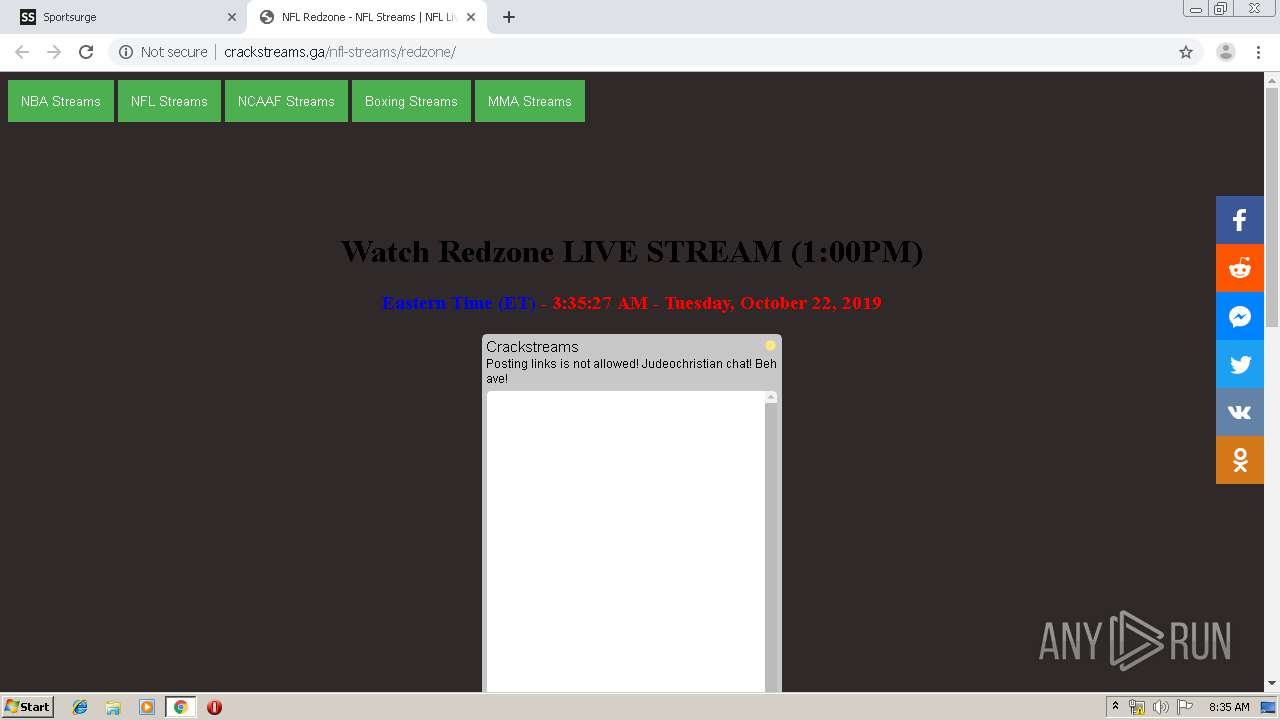
Malware analysis: Hands-On Shellbot malware – Sysdig
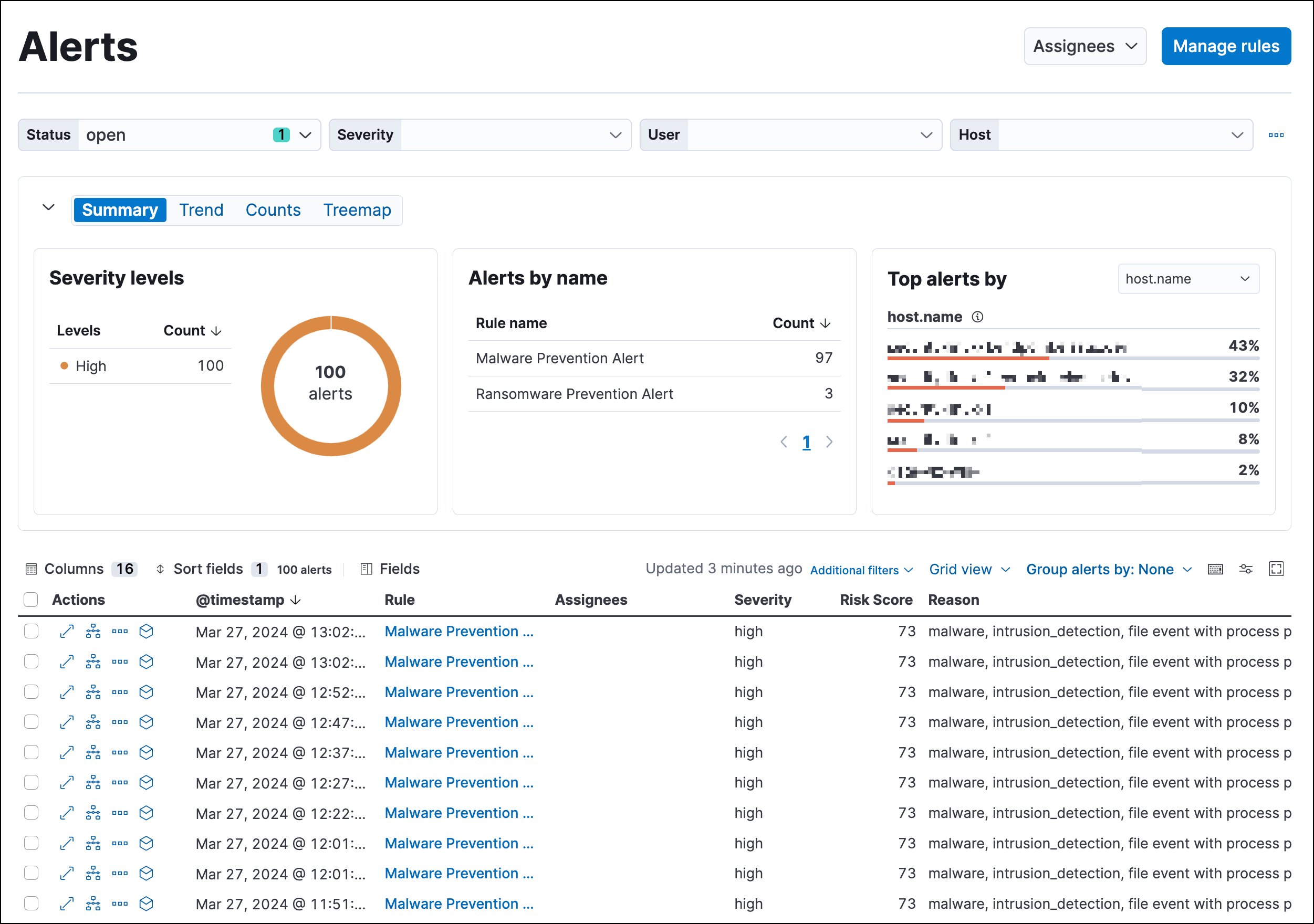
Detections and alerts, Elastic Security Solution [8.10]

Advanced Malware Analysis Training - Detection and Removal of

What is Malware Analysis
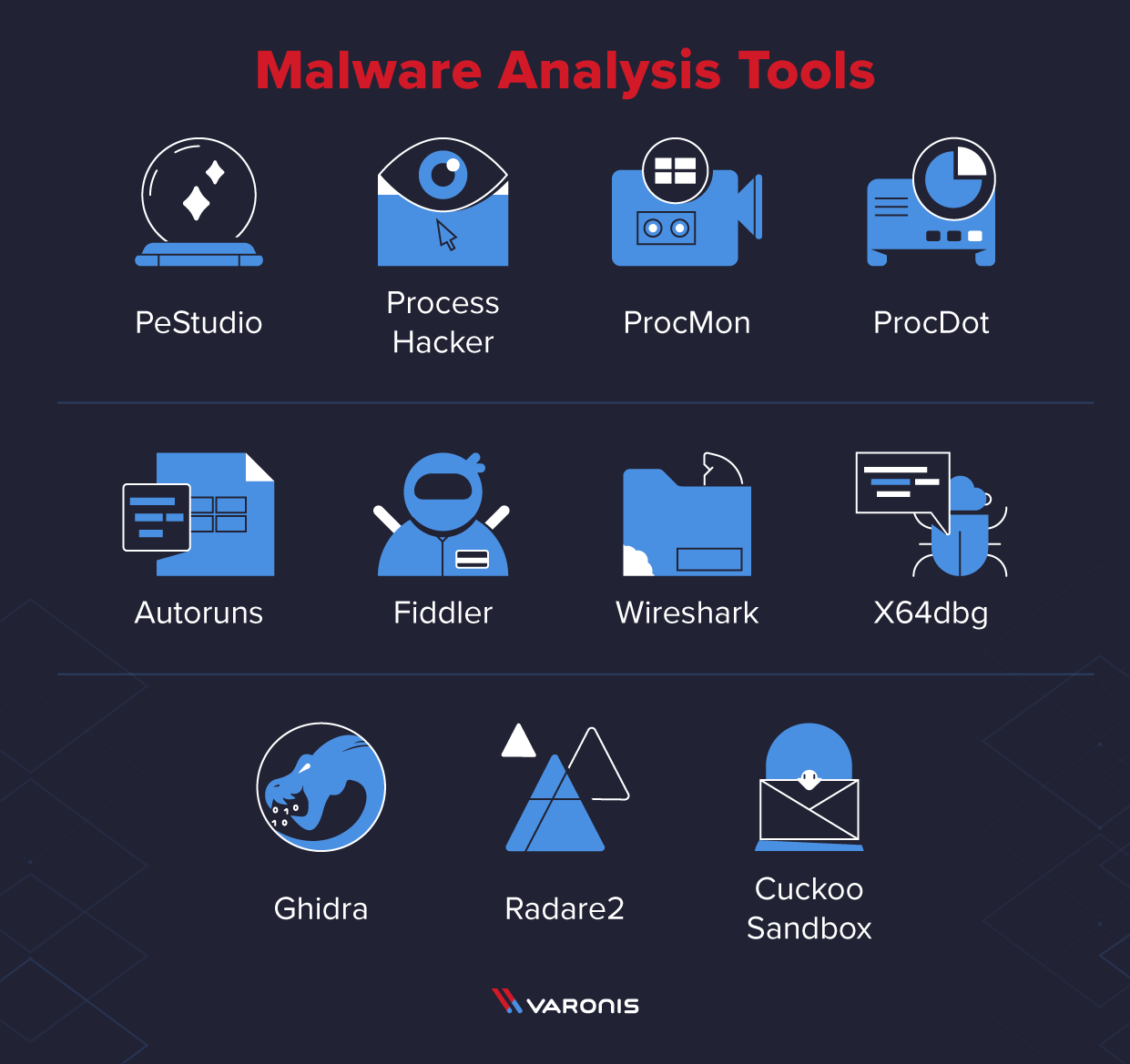
11 Best Malware Analysis Tools and Their Features
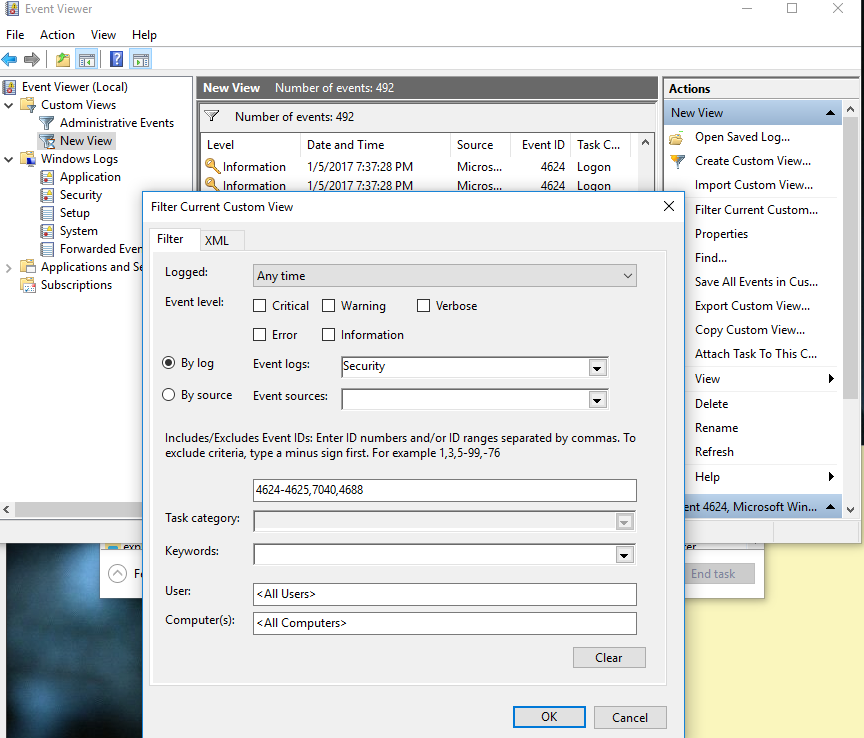
Malware Incident Response Steps on Windows, and Determining If the

How Malware Analysis Works - NetWitness Community - 669511

Malware Analysis Benefits Incident Response