Malware analysis Malicious activity
4.8
$ 23.50
In stock
(464)
Product Description

What is Malware Analysis
Highlight, take notes, and search in the book

Mastering Malware Analysis: A malware analyst's practical guide to combating malicious software, APT, cybercrime, and IoT attacks, 2nd Edition

Malware Analysis: Steps & Examples - CrowdStrike
Process flowchart of the malware analysis process during the experiment

Is Malware Analysis Right for Your Business?

What is Malware Analysis? Types and Stages of Malware Analysis

Election Security Spotlight – Malware Analysis
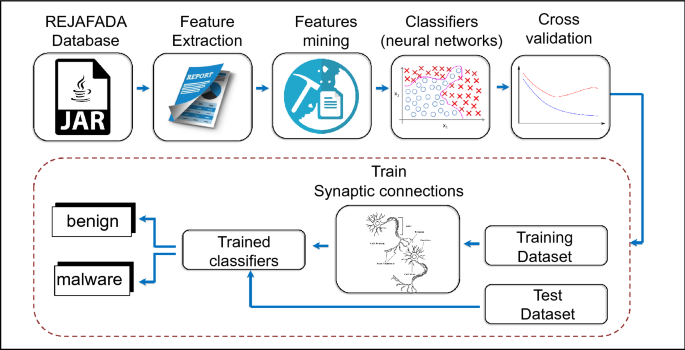
Antivirus applied to JAR malware detection based on runtime behaviors
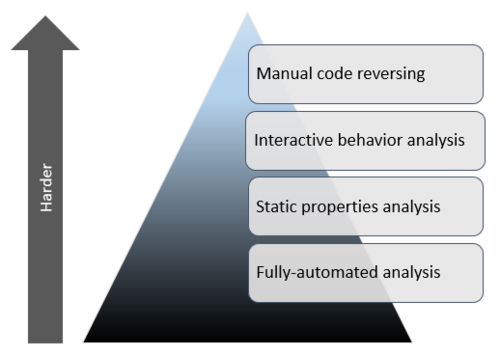
Mastering 4 Stages of Malware Analysis
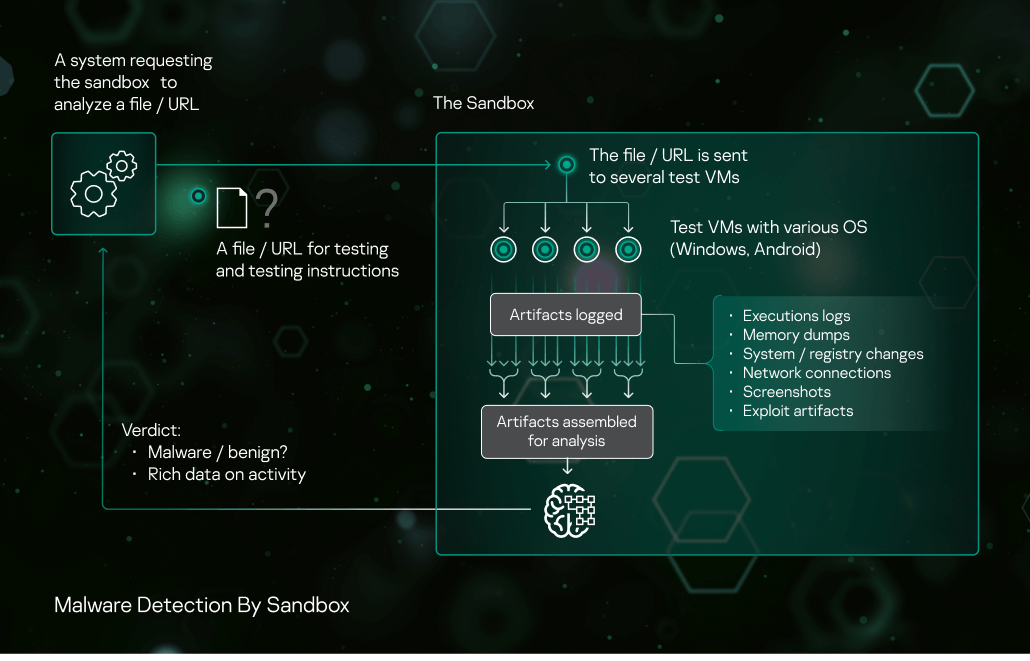
Sandbox Kaspersky
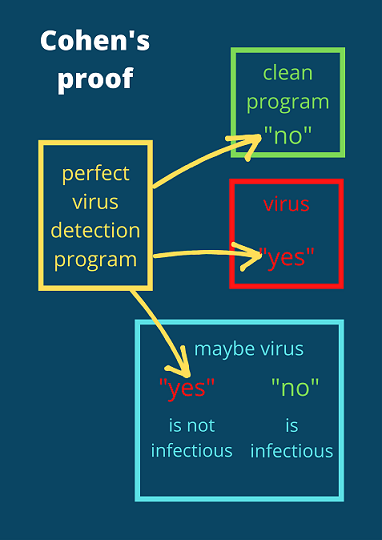
The real reason why malware detection is hard
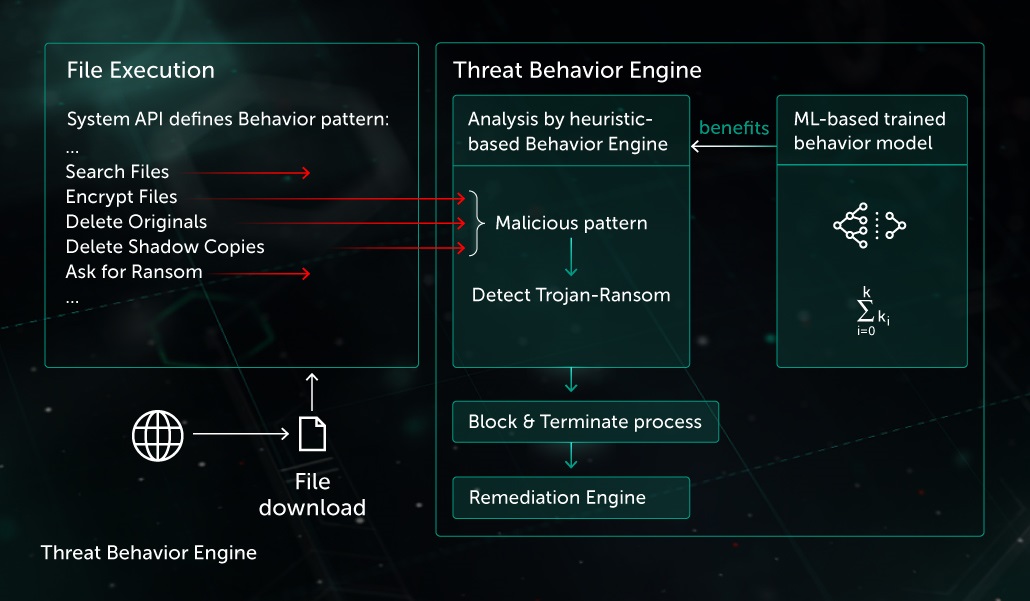
Behavior-based Protection

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights